
Is your VPN blocked at school, work or your favorite streaming platform?
Virtual Private Networks are the perfect tool for unblocking content and staying secure online, but that makes them targets for firewalls and blacklisting too.
There are several reasons your VPN service might be blocked. You’ll learn why you’re VPN is blocked and the most effective methods to bypass VPN blocks.
Best VPNs to bypass VPN Blocks
These are the best VPNs for bypassing firewalls and vpn blocks. They offer advanced features that helps them evade firewalls, packet filtering and other VPN-detection technologies.
They offer unique features such as stealth protocols, VPN over Tor, and dedicated IP addresses to make sure your VPN works almost anywhere.
- NordVPN – Obfuscated servers and VPN-over-Tor
- Private Internet Access – Stealth protocol & smartDNS
- IPVanish – Obuscation, Huge IP address pool
- Cyberghost – Obfuscated servers
- VPN.ac – stealth protocol
Why are VPNs blocked?
There are several reasons VPN traffic might be blocked on a network, service, or website.
These are the most common reasons.
1. School & Work
Schools, universities and employers often block VPN traffic. There are a variety of reasons they might elect to do so. In general in boils down to a few things:
- Distraction – If your network admin blocks social media apps and streaming sites to keep you focused at work or school, it makes sense to block circumvention technologies as well.
- Security – Because VPNs are encrypted, packet filtering technologies like DPI don’t work. This can prevent a cybersecurity risk, especially at the office.
- Liability – Some VPN uses can have legal risk, such as torrenting copyrighted files.
2. Licensing & Copyright

Many streaming services try to detect and block VPN usage. Netflix, Hulu, and Disney+ are a few examples of streaming apps with anti-VPN technology.
Content licensing is incredibly complicated and usually has different contracts for each geographic region. Because VPNs let you access content from multiple regions, they’re often targeted by streaming platforms.
VPNs may also be used to evade restrictions on account sharing by people that don’t live in the same location. This is something Netflix is cracking down on recently, asking account holders to pay for their shared accounts.
Fortunately, many VPNs have built workarounds that evade Netflix’s detection technology. Even better, such usage isn’t likely to be illegal, merely a terms of service violation.
3. Censorship
Government censorship is widespread outside of western democracies. You’ve no doubt heard of the ‘Great Firewall of China’. Numerous authoritarian regimes around the world attempt to limit access to information as a form of control. This extends to VPN blocking, which can be used to circumvent firewalls.
China isn’t the only country doing this. Russia, Belarus, Iran, Iraq and Turkmenistan are a few examples of countries that have declared VPN usage illegal. Others like Turkey, China, UAE and Venezuela are using firewalls and blocking technologies instead.
4. Fraud & Abuse
Bad actors use proxies & VPNs for DDOS attacks, fraudulent credit card purchases, online theft and other forms of fraud. They use the anonymity and database of IP addresses to commit crimes.
Even though this is a tiny minority of VPN users, many financial and e-commerce sites have taken steps to block VPN connections, especially for users that aren’t logged in.
Examples of sites that have (or currently do) limit VPN traffic:
- Banks (blacklisted IP addresses)
- Forum sites
- Payment processors – Stripe, Paypal, Braintree
But here’s the good news…
Blocking VPN traffic requires identifying VPN traffic. Fortunately, there are several techniques you can use to disguise VPN traffic, making it almost unblockable.
How VPNs are Blocked
Network admins use multiple techniques to block VPNs and other encrypted traffic. These are the tools you’ll see most often:
Port Blocking
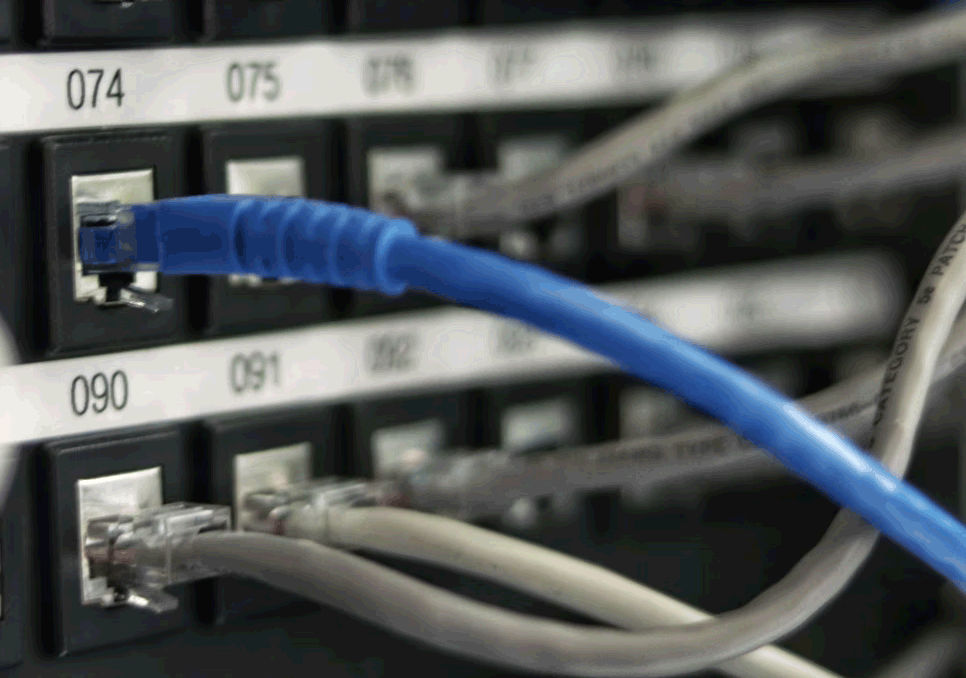
VPN protocols like OpenVPN often run on the same default ports: 443 for TCP and 1194 for UDP traffic. If a firewall blocks these ports entirely, any VPN running on exclusively on those ports will be blocked as well.
Fortunately, full port blocking isn’t used very often, especially for port 443 which is also used by all SSL traffic (the encryption that protects all secure websites).
Bypass port blocking: Switch to a different tunneling protocol or non-standard port.
Deep packet inspection (DPI)
Even though VPN data packets are fully encrypted, they still contain metadata the tells intermediaries (like your ISP) where to forward them to.
Some VPN protocols even use default data packet headers that allow firewalls fingerprint VPN packets.
Firewalls use advanced software to perform this analysis. IT professionals call this Deep Packet Inspection (DPI) which can analyze the type and destination of every data packet traversing the network.
Deep packet inspection is what allows your ISP to tell the difference between youtube, web browser, VPN, skype or any of 1000+ other types of traffic. DPI is how a network can throttle, restrict, or even block certain types of traffic.
But here’s the key: If you can disguise your VPN traffic as regular web browser traffic, you can make it impossible for a network to block your VPN (unless they’re willing to block all https browser traffic. Not likely).
Bypass DPI: Use stealth protocols to obfuscate packet headers and circumvent fingerprinting.
Blacklisted IP addresses
VPN services rent huge pools of IP addresses which are shared among users with active VPN connections. Often these IPs are from the same ‘c-block’ of IP addresses, e.g. 100.65.192.1, 100.65.192.2 etc.
Services like Netflix attempt to identify which IP blocks belong to VPN traffic and then block those IP’s from streaming. Smaller companies can use 3rd-party IP blacklist databases provided by data brokers and cybersecurity consultants.
Blacklisting is the primary technique used by web-facing services and websites to block VPN traffic since they don’t have access to the raw packet data (like your ISP does).
Bypass IP Blacklisting – Switch to VPN servers, use dedicated IP addresses, use a VPN with integrated SmartDNS
How to Unblock a VPN
To combat VPN blockades, VPN providers have developed sophisticated workarounds to circumvent nearly every technology used by firewalls and websites to detect VPN traffic.
It’s important to choose the correct circumvention technique to match the blocking technology being used and the type of service or firewall that is blocking VPN traffic.
Recommended circumvention techniques:
- Switch server / IP address
- Change the VPN protocol or port
- Use obfuscation (stealth protocols)
- Use SmartDNS
- Get a dedicated IP address
- Change DNS servers
Change VPN Servers (new IP address)
Works for: sites and apps that block VPN usage. If it’s a streaming service (e.g. Netflix) you’re better off using SmartDNS.
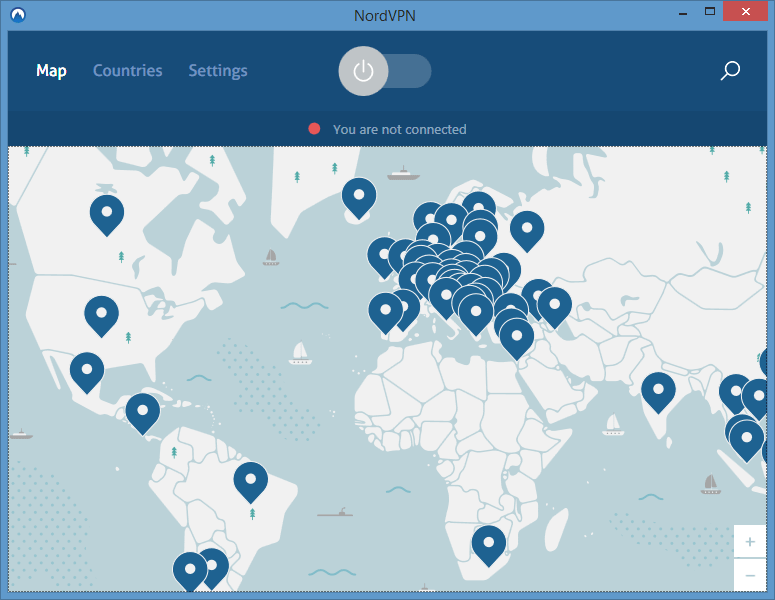
If you’re getting a VPN error from a specific website, service or app, there’s a good chance your IP addresses is in their blacklist database.
Sometimes, simply switching VPN servers will do the trick, which should put you in an entirely new block of IP addresses. Companies like NordVPN and ExpressVPN offer well over 100 unique server locations.
It’s a good idea to use a server location that matches the app’s visitor demographic. So if you’re visiting a US website, use a server based in the USA. Your Lithuanian IP address looks suspicious.
You may have to try a few different locations until you find an unblocked IP address. If you’re still blocked, try clearing your browser cache & cookies or using a different browser altogether.
Switch Protocols
Works for: Firewalls that block specific ports or VPN protocols (work, school, public wi-fi, in-flight)
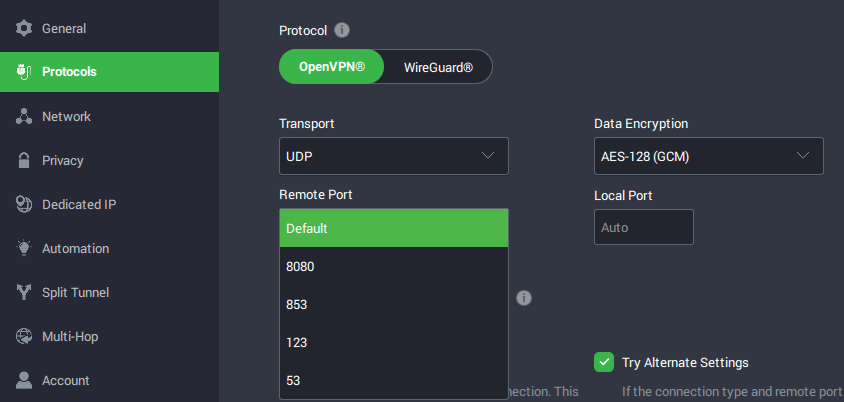
By default, most VPN apps use the OpenVPN UDP protocol on port 1194. OpenVPN is pretty obvious with its footprint and is easily blocked by even basic firewalls.
If your VPN app offers it, try switch to OpenVPN TCP which usually runs on port 443 (the same as HTTPs web traffic). This makes it harder to block with port-based blocking.
If that fails, switch to a different protocol altogether. L2TP/IPSec is a good backup option, though you may have to setup a manual connection to use it. Recently, many VPN providers are offering the Wireguard protocol which isn’t targeted by as many firewalls as OpenVPN and is harder to fingerprint.
Wireguard VPNs: Private Internet Access, NordVPN, ExpressVPN, Cyberghost.
VPN providers are aware that some ISPs/networks are blocking VPN traffic. That’s why they invented ‘Stealth’ VPN technology.
A stealth VPN can disguise/scramble your VPN traffic so it’s either not identifiable as VPN traffic, or even better — disguised as regular TLS encrypted web traffic.
Here are the two tried and true techniques to unblock your VPN service on almost any network:
Obfuscation (stealth VPN)
Works for: Firewalls that detect VPN traffic (ISP, School, Work, public wifi)
Protocols like OpenVPN don’t have to use default ports. Nor do they need to use the default packet headers that make them vulnerable to Deep Packet Inspection.
Lots of VPN apps now include stealth protocols or other obfuscation techniques that help disguise VPN traffic and make it harder to block.
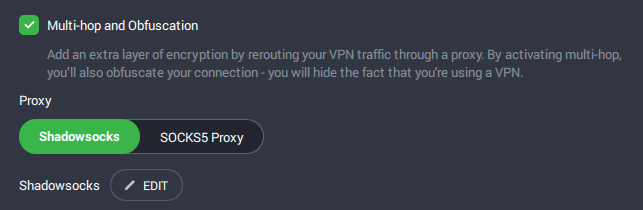
Enabling this is usually as simple as turning obfuscation on in the VPN software (as with IPVanish) or switching to an obfuscated server (NordVPN).
VPNs can use multiple Obfuscation techniques, such as:
- changing default packet headers
- Add additional SSL encryption (disguise OpenVPN traffic as https traffic).
- Route through an encrypted proxy (e.g. ShadowSOCKS)
Obfuscated Protocols: VPNs like IPVanish and VPN.ac offer obuscation as an in-client option that you can easily toggle on, regardless of protocol.
Some companies have even built stealth protocols from the ground up. Vypr VPN offers their excellent Chameleon protocol (based on OpenVPN) which even works to bypass the Chinese great firewall.
Obfuscated Servers: Other companies have dedicated servers with anti-blocking technology. All you have to do is a choose a compatible server in your VPN apps server selection view. NordVPN and Express VPN are two companies with obfuscated vpn servers.
Also read: The Best stealth VPNs
SmartDNS
Works for: streaming services like Netflix, Hulu, NFL Sunday Ticket, HBOMax
If you want to access websites and streaming services like Netflix, you’ll need more than a simple VPN connection. These services use IP-blocking blacklists, network heuristics and other sophisticated strategies to detect VPN usage. Simply switching IP addresses isn’t going to cut it.
Instead, choose a VPN that uses an integrated smartDNS proxy to bypass VPN-detection algorithms. In fact, you don’t even need to use a VPN at all. Services like ExpressVPN’s mediastreamer DNS can be configured directly on your router, PC or mobile device.
SmartDNS works seamlessly behind the scenes and uses a secret pool of non-banned IP addresses for the initial authentication checks when you access a compatible streaming platform. It’s an elegant way to bypass VPN blocking.
VPNs with built-in SmartDNS: NordVPN, Private Internet Access, ExpressVPN.
Static / Dedicated IP Address
Most VPNs use pools or shared IP addresses, where you’re sharing a single IP address with dozens of other users. This type traffic often appears suspicious to websites and makes it easy to identify which IP blocks belong to VPN providers rather than residential traffic.
Some VPN services offer dedicated IP addresses, where you get your own unique IP that belongs to use you. These IPs are unlikely to be blacklisted and won’t have suspicious usage heuristics that you get with shared IPs.
Static IP addresses are usually a paid upgrade ($3-5 per month). VyprVPN even lets you deploy your own dedicated VPN server to a cloud VPS server which you can access using their app.
Switch to Mobile Data
Instead of using a firewalled wi-fi connection, just user your mobile data from your smartphone. You can even use the hotspot functionality or USB tethering to share your internet connection to other devices. This is perfect for streaming to your laptop at school if the school network is blocking VPNs .
Also read: How much data does a VPN use?
Change DNS
If your VPN doesn’t provide its own secure DNS servers, you’re likely using the default DNS provided by the network you’re connected to. These could leave you vulnerable to VPN blocking, even on simple consumer router models.
Instead, you can force your device to use 3rd-party (free) DNS services such as GoogleDNS (8.8.8.8, 8.8.4.4) or Cloudflare (1.1.1.1, 1.0.0.1).
This technique will only bypass the simplest of firewalls, but it’s a completely free tweak (and good privacy practice) so it’s worth a shot.
Also see: this list of Free DNS servers.
Advanced Obfuscation Techniques
If you’re trying to circumvent a sophisticated firewall, the above methods to circumvent vpn blocks may not work. In that case, you can try one of these advanced obfuscation techniques.
VPN over Tor
NordVPN is one VPN provider that offers a VPN server that tunnels your VPN through the Tor onion network. This is a network of encrypted, anonymous proxies that help obfuscate the VPN data packets themselves, not just the headers.
Tor was built from the ground up as an anti-censorship and privacy tool, and it makes it nearly impossible for an endpoint or middle-man to identify the original source of the traffic.
In our testing, Tor routing is quite effective at bypassing VPN blocks.
VPNs with VPN-Over-Tor Support
ShadowSOCKS
ShadowSOCKS is like a lightweight version of Tor, but doesn’t rely on a 3rd-party network of volunteer proxy nodes. Instead it’s a client that allows user (or VPN services) to tunnel to an encrypted proxy server over SSH. ShadowSOCKS can effectively transport and obfuscate UDP traffic such as OpenVPN.
Compared to Tor ShadowSOCKS offers faster speeds but may be less effective at bypassing the most advanced firewalls because it isn’t resistant to active probing.
Nevertheless, it’s proven highly effective at bypassing the Great Firewall and other national blockades.
Supported VPNs: Private Internet Access now includes a Shadowsocks option directly in their VPN app.
How to know if your VPN has been detected?
Websites that blacklist VPN usage are pretty transparent about whether they think you’re using one. For example, Netflix displays the famous ‘Netflix Proxy Error’ message if they detect your VPN connection.
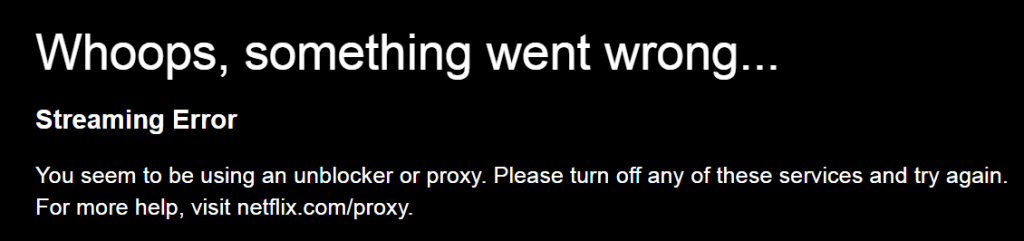
Other streaming apps aren’t quite so blatant but usually display an error message to the effect of:
“This content cannot be streamed in your region”
– Love, Hulu
And finally, some sites display no message whatsoever, they simply deny access. For example, I found that my online bank account would reject all my login attempts when connected to a certain VPN service.
Summary and additional resources
We’ve learned 3 different ways to unblock your VPN on any network, and get through any firewall.
The easiest solution is often the best, and you’ll find 90%+ success by using either OpenVPN on port 443, or a VPN with built-in obfuscation technology.
And if after exhausting all options you still find yourself blocked, then go with obfsproxy and Tor as the ultimate unblocker.
More useful articles and guides:
- Learn how VPN encryption works
- Why your passwords AREN’T strong enough
- The best VPN-capable wireless routers


Great site/info, I wish I found it sooner.
Also wish there were more sites like this for other techs, oh well.
Love hearing positive feedback. Glad we could help!
Agreed!!!
I’m using a vpn at work right now which was blocked until I read this article
Any free vpn
I don’t recommend any so-called ‘free’ VPNs, because they’re monetized through other methods that undo any privacy benefit. There are a few paid services that offer a free tier, with limited bandwidth or speeds. Windscribe is a good option and allows up to 5G free data with an account.
my parents installed MyCircle on my internet, and the only vpn’s I can currently use are browser extensions, which generally only last less than a day before my parents block the ip. Do you have any good vpn extensions?
I have my parents blocking all the ip’s for each vpn, do you know any good extension vpns?
Browser extensions aren’t true VPNs, more like an encrypted proxy for your web browser. So it will only anonymize browser traffic. NordVPN, Torguard, and Private Internet Access all have browser extensions. You also might try Opera VPN which is free and built into opera web browser.
Also Hide.me VPN has 10GB of free data per month, and has a browser extension. FYI, your parents’ firewall may be blocking OpenVPN traffic, rather than the IPs of the servers. Try a stealth protocol or enable obfuscation if your VPN supports it.
And stay away from most ‘free’ proxy extensions. A lot of them are malware.
my school has all of your links blocked? what do I do?
You can try using tor or an https proxy like kproxy.com. If those are blocked to, you’ll have to install the VPN while on a different network (not your school).
Interesting article, but I couldn’t find anywhere obfsproxy, is it deprecated? I already have an OpenVPN server on pfSense, is it possible to use obfsproxy with it?
Take that shitty library wifi!
Thanks guys, great info, super helpful!
This could be helpful for the future but it wasn’t helpful for me as of now. While my school has personal chrome book computers, I’m only trying to play apps on my phone using the school’s wifi. I used to use vpn apps like ultra surf, but recently it stopped working. What I need is a solution that will work for mobile.
Several of the VPNs in this guide as well as our stealth VPN tech article have mobile apps (iOS and Android) as well. IPVanish would be a good choice as they have a mobile app for both platforms with a built-in obfuscation option to get through firewalls.
none of these vpns worked for me all either says its blocked or says connection cut but only when i go to those sites
Do you mean the VPN sites themselves are blocked?
Yes my school has blocked these sites as well
which is the best for mac pro?
The choice of VPN depends mostly on what you want to use it for, not what platform you’re on. Why do you want the VPN?
I live in the UK and just need a VPN to access some blocked sites. dropbox.com fr instance.
I need it to do some work, so I signed up for hidden24co.uk but I cannot connect to it.
Tried it on my MacBook Air and my iPhoneX
Can’t connect to dropbox? Or the VPN?
I want to use NordVPN at school and I use it at home personally, but when I try to install the software onto my Mac, it needs an admin password to connect…
Most VPN software requires admin rights to run, but NordVPN has an easy workaround. If you have access to the chrome web browser, you can try installing the NordVPN secure proxy extension which you can connect to using your normal NordVPN username/password.
I use Private Internet Access VPN and even your site blocked me. I thought, how ironic, being blocked from this article which was written to specifically tell people how to get around being blocked.
Luckily I was able to keep my PIA VPN connection active and use the Opera browser’s built-in VPN to access this site with a non-PIA IP address.
Curious, what do you have against PIA?
This site does not block PIA. In fact, I frequently use PIA while editing the site and replying to comments. Heck, I’m using it right now. You may have some other issue not related to your VPN at all.
I use Nordvpn because IMO it’s super important that a vpn would frequently add new servers as it makes it easy to find a not blocked one. Cooperative client support is also essential, for example, if you want to stream US Netflix – support can give you info about newer and better services to connect.
New NGFW can see TOR, and are now able to see the traffic on 443..
Do proxies work the same? I have access to Oxylabs.io proxies from my work wondering if I can use them for my trip to China this year.
It may work. Give it a try and let us know!
Great article! I use VPN a lot when travelling in order to access US Netflix.
It would be great if you could write an article about residential proxies like Smartproxy and how they work for scraping etc. I’m thinking of purchasing a service but there are way too many paid reviews that I don’t seem to trust and I myself don’t have the right expertise to determine whether Smartproxy would suit my personal needs.
I can’t connect to my vpn (nordvpn) no matter what I do on my school wifi. I had tried all of the above techniques but still it wont work. I can’t play games like World of Warcraft while waiting for band to start or etc thanks to the filter. Help?
You will want to use NordVPN’s obfuscated servers feature. Here’s their tutorial: https://support.nordvpn.com/General-info/1161436372/Connecting-from-a-country-with-internet-restrictions.htm
The site is really cool, but sadly, our school went to the point to block EVERY vpn. If there is a way to reach the vpns’ site, that would be great.
Can you connect a USB drive to your school’s PCs and run an encrypted browser like Tor portable? This should let you connect to the VPN sites.
MY SCHOOL SUCKS, BLOCKED EVERYTHING, thanks for the info though.
Nice article, a but too advance for me; I am a simple guy…. Tried to use a VPN and got blocked each and every time trying to log in any of my banks. Tried different servers (even ones located in my home city) but to no avail. So while I tried to be more safe as I am using public wifi, the final outcome is that I can’t do ANY online banking…. Any ideas? (as I said- ideas for a simple guy, without re configuring all my proxies/ports/protocols
Nice article, a but too advance for me; I am a simple guy…. Tried to use a VPN and got blocked each and every time trying to log in any of my banks. Tried different servers (even ones located in my home city) but to no avail. So while I tried to be more safe as I am using public wifi, the final outcome is that I can’t do ANY online banking…. Any ideas? (as I said- ideas for a simple guy, without re configuring all my proxies/ports/protocols
Your bank’s website certainly uses https which encrypts all the text you type (like passwords) with a cipher similar to what your VPN uses. Bottom line: feel free to simply log-off your VPN when you need access your bank account, even on public wifi.
Hi guys
Indian goverment has imposed restrictions on social network like youtube facebook whtsapp etc the have created firewall we used everyvpn and after each day vpns get blocked right now only anonytun works only on andriod but that app is not avaiable on iphone and the goverment hs also limited the internet speed to 2g low speed internet we are not able to download nor surf social media only we can access goverment sites
even the ones wo paid for vpn they too havebeen blocked after some time
can u suggest any method so that we can atleast have our right to use internet.Any method for iphonr to surf socials when vpns are also blocked and firewall is there
it wuld be helpful if u can step by step tell me what to do
thanks
from
KASHMIR
You may have luck using a VPN that has stealth/obfuscation technology. It tries to disguise VPN traffic to get through firewalls.
VyprVPN reportedly works in China which has a very powerful firewall, so that may be a good choice. There are also 2 VPNs you can test completely free to see if they work:
I am from Kashmir (India). Our have blocked internet service since August 4. Now, a month ago they have restored 2g network without social media access. We ran vpn for month but now it’s blocked by a firewall… Plzzz help us
Try using a VPN that has stealth technology to get around the firewall.
I know nothing about any of this. Can you please help to use Google Voice, WhatsApp, and Google Chrome (or anything at all) through the Jpay WiFi provided to prisons?
I’m not knowledgeable about the specific firewalls prisons use, but I expect there are extra strict rules on circumventing them. I can’t recommend any tactics or write a tutorial on that.
Hey,
My school blocked most of the common VPNs I use like Proton etc. I’ve tried Hide.me and Windscribe but they do not work. Is there some sort of good free VPN that can at least let me access websites I want to access like discord etc? if there aren’t is there anything I can change in my vpn setting for windscribe, proton or hide.me?
Thank you
Many free VPNs are worthless or legitimately dangerous. You could try 1.1.1.1 which is completely free and has VPN-like functionality. It’s owned by Cloudflare which is a large, reputable company.