The U.S. Senate and house of representatives just voted to roll back privacy protections implemented by the FCC, designed to protect user privacy.
The issue in question is what exactly your ISP (internet provider) is allowed to do with the treasure trove of data they have about you and your online activity.
For example, can they:
- Monitor your online searches and web history
- Inject ads into your browser traffic
- Hijack and redirect your DNS requests
- Inject ‘SuperCookies’ to allow advertisers to track you across the entire internet
- Sell you internet history (and personality profile) to the highest bidder
This Obama-era privacy was designed to go into effect soon, requiring ISP’s to take ‘reasonable’ care when protecting your data. So much for that.
It looks like it’ll be a wild-west style free-for-all. And your data is what’s on the auction block.
How big a deal is this?
Huge. Enormous.
It’s hard to overstate the privacy concerns regarding this new policy.
The reason is simple:
Our entire lives are online!
Think hard about what your internet browsing and search history says about you. Someone who had unfettered access to it (combined with incredibly powerful ‘big data’ analytical tools) would know:
- Your hobbies
- Your financial status
- Social and political views
- Your approximate net worth
- Age, gender, sexual orientation
- Brands, products, and websites you love
- Your usernames on ‘anonymous’ websites (reddit, twitter, forums)
- Medical conditions or concerns
- Your deepest darkest secrets and fears
Now imagine any business on earth can directly market to you based on that data…
Search for ‘what does herpes look like’ and get bombarded with junk mail selling miracle ‘solutions’.
Visit a progressive (or conservative) website, and be forever put into a political database that can be matched against your facebook and twitter profiles.
And don’t think that only U.S. companies will be the ones buying your data.
You won’t know who your data was sold to, and you’ll have no control over it whatsoever.
What could your ISP do with your data?
There are a number of likely ways your ISP will attempt to monetize your identity and internet history (many of which are already happening, but would’ve been banned under the previous law).
Monitor every website you visit
Your internet provider can (and probably already does) use techniques like Deep Packet Inspection and Transparent DNS Hijacking to see which websites you’re visiting and what you do online. DNS lookups routed through your ISP’s own DNS servers provide them with a complete list of every website you visit.
Privacy Risk: Medium
Internet Providers doing this already: Most, if not all US-based ISP’s have their own DNS servers and may log your web history. This includes Verizon, Comcast, Time Warner, At&t etc…
Hijack your searches
If you visit a search engine directly (such as google) your searches are protected with https encryption, so your ISP can’t see them directly. However, ISP’s can hijack any search that is typed directly into your browser’s url bar. Most of us do this for the majority of searches (convenience).
Before redirecting your search to your preferred engine, the ISP first route the query to a middle-man like Paxfire to intercept and log your search query before allowing google to deliver the actual search results. The EFF (and others) have reported extensively on widespread search hijacking in the USA.
Privacy Risk: High (just think what your searches say about you)
Internet Providers who have done this: Charter, Cogent, Frontier, RCN (Source: EFF)
Inject ads into your browser
As if the internet wasn’t already littered with ads, some ISP’s are using their treasure trove of data on your shopping preferences to inject even more ads into your browsing traffic, using a process called ‘Deep Packet Inspection’. It’s like Ad-blocking in reverse, and it’s been done by companies including Charter and AT&T
Privacy Risk: Medium-Low
Internet Providers who have done this: Charter, AT&T, Comcast
Inject ‘Super Cookies’ to let advertisers to track you everywhere
ISP’s, including the nation’s two largest mobile providers (AT&T and Verizon) have started using ‘Supercookies’ that attach a unique identifier tag to 100% of your internet traffic that flows through their servers.
Normal cookies are individual per-website cookies that areonly accessible by that one website (and can be blocked or deleted by the users).
SuperCookies, by contrast, are a snippet of code that is attached to the header of ALL data packets as they flow through your ISP’s servers. They use a UIDH (Unique IDentifier token Header) that specifically identifies your unique traffic across all websites.
This allows advertisers to track you even after you leave their website. But that’s the least of your worries.
Imagine what a nation state (think: Russia) or the NSA could do with those super cookies. Your every virtual move can be tracked with absolute precision, and stored indefinitely for later retrieval.
Privacy Risk: MAXIMUM
Internet Providers who have done this: Verizon, AT&T, likely others…
But don’t give up hope just yet. There are steps you can take to reduce (possibly even eliminate) your ISP’s ability to collect this type of data about your browsing habits.
Fair warning, it may add $5-10 to your monthly internet bill (not paid to your ISP though :-), but it will be money well spent.
Steps to protect your privacy (and stop ISP spying)
Though the privacy risk listed about sound terrifying (and they legitimately are) your ISP has to rely on one thing within your control in order to implement them:
They need complete, unfiltered access to your data stream and traffic
Now I know this seems obvious, and most people will point at out that since they are the internet provider, of course they have access.
And you’d be right…
As long as you choose not to encrypt your traffic.
But you as a consumer have both the right, and the ability to easily encrypt all your internet traffic, even before it flows through your ISP’s network of data inspection (and injection) tools.
It’s called a VPN (Virtual Private Network), and privacy-conscious people (like us) have been using them for years.
And the best part: high-quality VPNs can be had for under $4 a month.
Here are the steps you need to follow to take back your privacy…
Encrypt your traffic so your ISP can’t snoop
Method #1 – VPN (best option)
Subscribe to a reputable VPN service (like those featured on this site) and download their software. Plans run between $4-$12 month depending on the company you choose and the length of your subscription. 1 or 2 year subscriptions come at a huge discount (50-70%).
We recommend choosing a US-based VPN company, as you’re much more likely to get exactly what you’re paying for (they’re legally accountable for their promises). Also, since data retention laws don’t apply to VPNs inside the USA, several VPN services choose to keep no logs whatsoever.
Best Bets:
- Private Internet Access |read review| – $3.33+ per month
- IPVanish |read review| – $6.49+ per month (25% off coupon)
- VyprVPN |read review| – $6+ per month w/ free trial
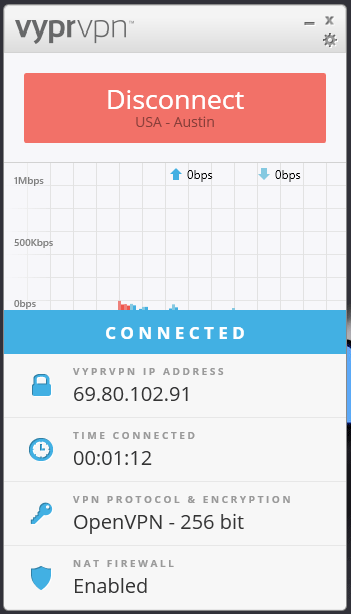
How to use the VPN
After you sign up, you’ll be sent a link to download the VPN software onto your device. The above VPN companies have custom apps for all major platforms, including Windows, Mac, iOS & Android.
You can even setup a VPN on your VPN-enabled router, and protect your entire network at once.
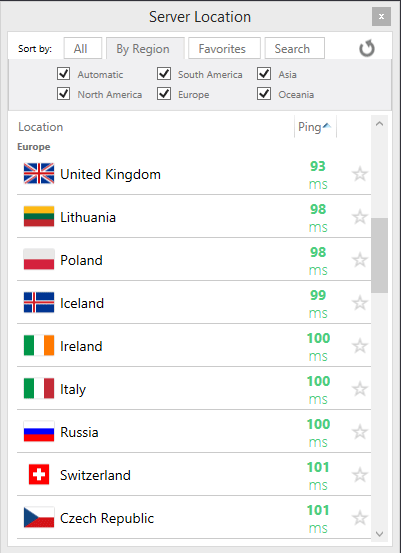
Simply:
- sign into the software using your VPN username/password
- Choose a server location from the list (usually you’ll want a nearby USA server)
- Click connect
- Success. The VPN will assign you a new IP address and encrypt your traffic.
Important: Don’t use ‘Free’ VPNs
There is no such thing as a free lunch, and VPNs are no exception. Bandwidth costs money, so if a VPN is made available for free, you should assume that 1 or more of the following is true:
- They are selling your browsing history (just like your ISP)
- Injecting ads (just like your ISP)
- Running malware on your computer, stealing data, or selling your bandwidth (like Hola).
Don’t cut corners to save a few bucks when it comes to your privacy. It’s not worth it.
What it will do:
The VPN uses extremely strong encryption (either 128-bit or 256-bit AES usually) which will wrap 100% of your internet traffic in an encrypted layer that prevents your ISP from seeing what it contains.
The VPN server will then pass any requests onto the websites you visit, and encrypt website responses for transmission back to you. This will help defeat browsing monitoring, ad injection, and super cookies.
You can either install the VPN on individual devices (get a VPN that allows simultaneous connections), or protect your entire network at once with a VPN router.
Method #2 – Tor Browser (free, w/ drawbacks)
If your primary concern is keeping your browsing history private, you can use the Tor Browser (and Tor network) which is a free network of encrypted proxies, run by volunteers. Your traffic will be routed through multiple proxies, resulting in strong encryption and a high degree of anonymity (greater than a VPN even).
You can easily get Tor on Windows, Linux, or Mac by downloading the pre-configured Tor browser bundle. For android devices, use Orbot + Orfox to encrypt your web browsing. Android apps can be selectively routed through Tor using Orbot also (neat feature).
Pros: Tor is free, and highly anonymous
Cons: You will quickly discover that using Tor has many annoyances:
- Speeds are really slow, due to limited bandwidth and multiple node hops
- Many websites will ‘Captcha’ tor users (or block you altogether)
- Encrypts only browser traffic, not all internet traffic
Lock down your DNS servers
One way your ISP monitors your web history is by trying to force your DNS lookups to go to through their own DNS servers. DNS servers are like the internet’s phonebook, translating domain names (google.com) into IP addresses (175.53.36.94).
After enabling a VPN, you will want to protect against DNS leaks to make sure your ISP isn’t still intercepting DNS queries. You can easily check if your ISP is snooping on DNS requests at DNS Leak Test.
If you aren’t using a VPN, you should manually specify which VPN server your devices use, but manually configuring DNS servers on either your router or each device individually.
Keeping search/Google history safe
Your search history is incredibly private and should be safeguarded at all costs. Here are a couple tips:
- Consider using DuckDuckGo: Google makes most of their money by monetizing their massive stores of data collected on their users’ search history. DuckDuckGo on the other hand doesn’t store an search data, and doesn’t offer paid advertising whatsoever (so they have no incentive to sell your data).
- Don’t search straight from the browser URL bar: Some ISP’s use search hijacking to intercept your search queries. Either use an official browser extension for instant searches, or go to the actual search engine home page before starting a sensitive search.
- Delete your Google History: Google has implemented new privacy protections for users, and you can actually choose to delete your entire Google and Youtube search history. Here’s how.
This video will walk you through the process of deleting your google search data:
(Optional)additional privacy steps
Here are some more things you can do to enhance your online privacy. These steps may reduce the convenience of your online experience, but they can make a big impact in privacy.
Block cookies, or use Private Browsing mode.
You can turn off ‘cookies’ in your favorite web browser, but the easier way to do this is to always run your browser in ‘private’ or ‘incognito’ mode. This will keep cookies for the current session (so you don’t have to keep logging back in to a website) but all stored cookies will be immediately discarded after you closet he browser window.
Chrome lets you choose to use extensions and plugins even in incognito mode, so you won’t be without your beloved password manger.
Lock down social media accounts
By default, Facebook profiles are publicly visible and searchable. All twitter activity is public. These profiles are trivial to link to your browsing history (since your ISP has all the data) and they serve as a further data point to profile your personality or economic situation.
Learn to use twitter anonymously, max out your facebook privacy settings,
Use good password and security practices
This isn’t specific to the Broadband privacy law, but it’s the easiest way to keep your financial and personal details secure online. Use strong, unique passwords, store them in a password manager, and enable 2-factor authentication for your important accounts.
It’s all in our strong password guide.
Summary and action steps
Your elected leaders sold out your privacy. And potential fallout could be huge.
But you do have the ability to keep most of your browsing history and internet usage completely private and out of your ISP’s greedy hands.
- Encrypt your Traffic (VPN or Tor)
- Make sure you don’t use your ISP’s DNS servers
- Delete your google history (or use a more private search engine)
- Keep pressure on your ISP for privacy, transparency, and accountability
For help choosing a VPN, checkout our VPN reviews. I can personally recommend Private Internet Access and VyprVPN, due to their user-friendly software and responsive tech support.


