One of the nicest features VPN users discover when upgrading to ASUSWRT-Merlin is the policy routing and killswitch feature. On stock ASUSWRT, all devices will be routed through the VPN tunnel when it’s active.
On Merlin, you can choose which devices you want to use the VPN and which should ignore it. You can even tell the router to use (or skip) the VPN for specific websites.
On top of that, Merlin adds a kill-switch feature, which optionally lets you kill internet access to all VPN-routed devices if the VPN tunnel goes down. This will prevent data or your real IP address from leaking in the event of VPN failure. This is perfect for Kodi/Torrent fans.
This guide will show you how to take advantage of all these powerful new features…
Introduction to Selective Routing
The selective routing/policy routing feature is only available for OpenVPN client connections. So makes sure you have a working OpenVPN connection before starting this tutorial. If you need help, checkout our guide to setting up OpenVPN on Merlin firmware.
To turn on selective routing:
Go to the OpenVPN client settings for your VPN connection which is found at: Advanced Settings > VPN > OpenVPN Clients (top tab)
The interface looks like:
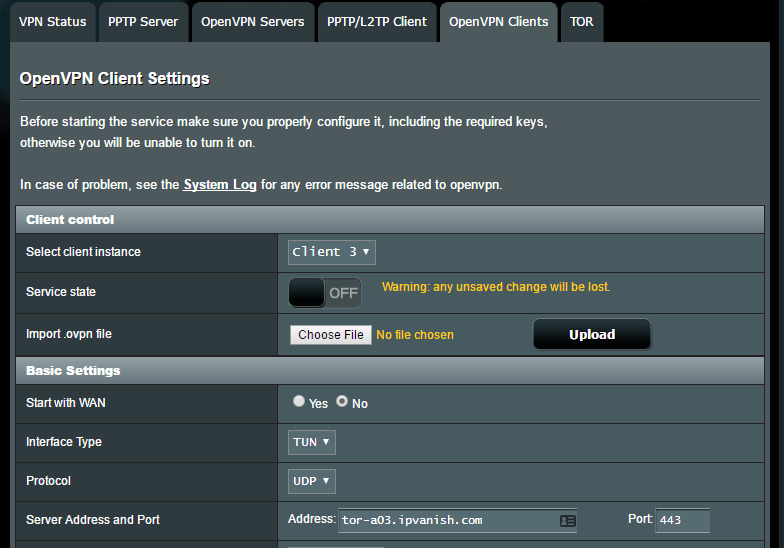
and all the way at the bottom you’ll find the option to turn on selective routing under the line ‘Redirect Internet Traffic.’
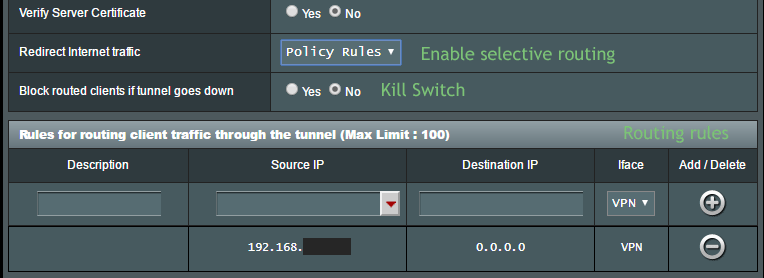
Once you change the setting to ‘Policy Rules’ it will create the dropdown box shown above with routing rules that allows you to add new devices or IP ranges to be routed inside/outside the VPN tunnel.
Setting routing rules
Basically you have types of choices:
- What to route
- Individual devices
- IP-ranges
- Where to route it
- VPN
- WAN (not VPN)
If you want most devices to USE the VPN…
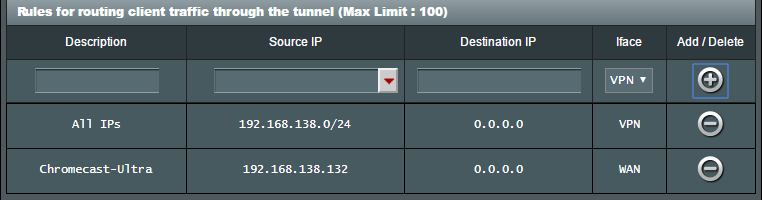
We’ll route ALL traffic through the VPN, then specify individual devices that won’t use the VPN.
To route all local IP’s through the VPN, we need to use CIDR Notation.
First, make sure you know what subnet your router’s DHCP is using. The easiest way to check this is to go to Advanced Settings > LAN > DHCP Server and look at the IP Pool numbers.
My router is using the 192.168.138.x subnet (my choice) but by default ASUS routers will use 192.168.1.x unless you’ve specified another one.
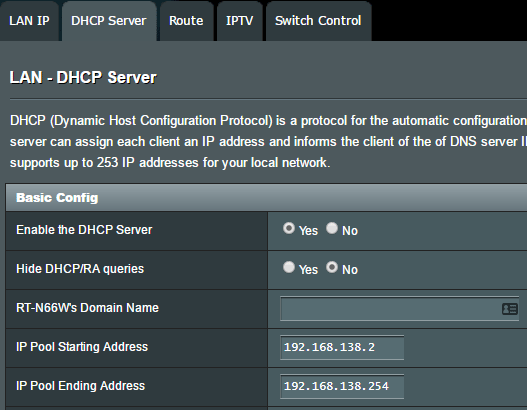
Once you know your subnet (the 3rd digit block), go back to the VPN routing settings.
To route all traffic in that subnet IP block through the VPN, type:
192.168.yoursubnet.0/24
so we did:
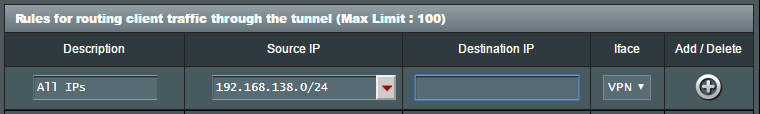
Then make sure to hit the ‘+’ icon in the Add/Delete column to actually add the rule.
Now you can manually add devices that will skip the VPN tunnel. For example, if you have a Chromecast and you want to be able to access Netflix (because your VPN is blocked), then you want the Chromecast not to use the VPN.
So click the arrow dropdown under ‘Source IP’ and your Chromecast will show up in the list as long as it’s currently connected to your router’s network.
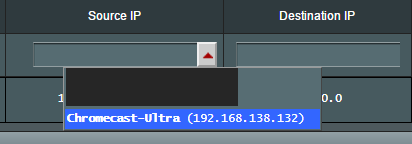
Then select ‘WAN’ as the Interface for that device, and click ‘+’ to add.
And now you have all local IP’s going through the VPN tunnel, except the chromecast which you told to go direct to WAN (bypassing the VPN).
If you want only a few specific devices to use the VPN…
If most devices will bypass the VPN tunnel, then you don’t need to route any IP blocks. Instead, just pick the individual devices you want to use the VPN, and manually add them from the Source IP dropdown. Choose ‘VPN’ as the Iface.
Using the Kill-Switch
Using the kill-switch feature in ASUSWRT is simple. Just change the following setting:
Block routed clients if tunnel goes down:
to ‘Yes’.
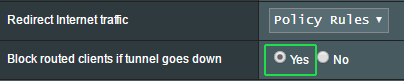
That’s it. If the VPN connection drops, none of your devices that you routed to the VPN will have internet access until you either:
- Turn the kill-switch off
- Restart the VPN connection
When to use?
So when should use these different kill-switch and VPN routing options? Here are some simple guidelines…
Route a device through the VPN if:
Any of the following are true:
- You use the device for sensitive transfers or transactions
- You need to bypass geo-restriction locks (such as accessing Netflix)
- You want full-time encryption or IP-address anonymity
Route a device outside the VPN if:
- You need to access a service that blocks VPNs
- You need maximum speed and don’t really need security (such as video streaming/gaming)
- Your comfortable with the device broadcasting your real IP address
- You often switch between VPN/non-VPN connections (instead, install the VPN directly on the device).
Use the Kill-Switch if:
It’s very important that your VPN-protected devices are never routed insecurely. Torrent/Kodi devices are two types that are frequently used with a kill switch. Also, if you’re accessing a service that may ban you if your IP changes unexpectedly (multiplayer games, online poker) you should definitely use a kill switch.
Conclusion
As you can see, ASUSWRT-Merlin’s kill-switch and routing capabilities are incredibly powerful. I consider it will worth the (minimal) effort to upgrade to Merlin and get this (and other) powerful features.
Not only do you get device-level control over VPN usage, but you literally eliminate and entire router (and $100-200 worth of cost) to have separate VPN and non-VPN devices on your home network.
If you have any other selective routing tips, comments, or questions…please share them in the comments below!


I have an ASUS RT-AC68U with firmware version 3.0.0.4.380_7743. Today, I went to install Private Internet Access OpenVPN on it. I started the same way as you by accessing the router’s control panel. I went to Advanced Settings > VPN > and the screen that displays for me is different than what you described above. I don’t see a screen with 6 tabs on top…one of them being the “OpenVPN Client ” tab you refer to. I only see 2 tabs: VPN Server and VPN Client. I went to the VPN Client tab, added a VPN profile and connected. My problem is It did not display any of the fields you had in your option like Start with WAN (which I’d like to turn off) and there is no way to activate the VPN kill switch which is what I want to do as I’m using the VPN with Kodi. How can I turn off Start with WAN and how do I activate the kill switch without these fields available?
This tutorial is for the ‘Merlin’ version of ASUSWRT which is a non-official 3rd-party firmware. The default (ASUS’s own) firmware doesn’t have these options.
try this done on ac68u with merlin
1- In the router go to VPN,
2- Go to OpenVPN Clients Tab,
3- Find “Advanced Settings”
4- Set “Redirect Internet Traffic” to Policy Rules
5- Below that you’ll see “Rules for routing client traffic through the tunnel”. Under Source IP I chose my IPTV box’s IP, left the “Destination IP” empty, set the “Iface” to Wan and clicked add and Apply. That’s it. Easy.
6- I chose to add all of my IPtv boxes, laptops and smartphones here and chose whichever Iface, Wan or VPN to suit my needs.
There’s also a kill switch here if you set “Block routed clients if tunnel goes down” to Yes.
Thank you! this helped me solve the same problem with a more recent version of merlin firmware. For the anyone still looking, it is indeed the last option in the ‘advanced settings’ section, but it’s now listed under the name
‘Force Internet traffic through tunnel’. Set it to policy rules and the you can continue as the tutorial explains above.
I set up this on my Asus rt-ac3200. flashed with merlin. ExpressVPN. everything went fine. No dns leaks. When I set up my Asus with the above settings and press apply, I immediately get dropped from the VPN. Internet works but VPN is down. It says its still connected in Merlin but Dns leak test shows nothing is working. I rehook up my VPN without settings and all is good again. For some reason those settings above are shutting off my VPN. Can’t for the life of me figure it out. Sucks cause I need a kill switch. It is the whole reason i went with this setup.
It sounds like your device is being routed outside the VPN tunnel, so you may have configured a setting incorrectly. Are you using the right subnet IP-range for your home network? Or did you manually specify your device. If you attach a screenshot of your settings I can try to help you troubleshoot. Otherwise, I expect the SNB forums are a great place to get assistance.
Is there a way to do policy-based routing with PPTP client (not OpenVPN)?
I have an ASUS RT88U and need pretty serious VPN BW (50M+) from Western Europe. I have found some VPN services but can only achieve this speed with PPTP, not ovpn…
I would like to only use one router and be able to do policy routing only for a few devices to use the VPN instead of std WAN, but does not seem available with PPTP.
Are there any smart workarounds?
Thanks !!
Unfortunately not. I’m not sure if that’s because of the architecture of the PPTP protocol, or if the developer didn’t think PPTP was used frequently enough to make building it worthwhile.
One suggestion: Have you tried running an openvpn VPN with 128-bit encryption (instead of 256-bit)? I’ve found the speeds to be reasonably close between pptp and AES-128
When using openvpn like you setup everything works great but the WAN address does not change. My problem is I am on a private IP from my ISP. XBOX gets a double Nat.
When I use PPTP my wan address become public ip but all devices running Netflix stop working due to my VPN being blocked by Netflix. Brand new to Merlin firmware any help would be greatly appreciated.
I use Purevpn
You can use the selective routing feature of merlin to route specific devices outside the VPN tunnel. So for example if you watch netflix on a Roku, you can tell Merlin to route that outside the VPN. If you are watching Netflix on a device that you want inside the VPN tunnel most of the time, your only option is to manually disable the VPN when watching netflix. Alternatively you could subscribe to one of these Netflix-compatible VPNs.
You covered setting up VPN based on device, but didn’t expand on how to do, “You can even tell the router to use (or skip) the VPN for specific websites.”
I live in a place where I can’t get local channels through DirectvNow, so I use my VPN to get them out of Chicago (using Merlin and routing my streaming devices through VPN). However, Netflix detects the VPN and doesn’t allow me to stream, so I’d like to exclude Netflix from going through the VPN. Any thoughts?
Unfortunately Netflix uses dozens of server IP’s and they change all the time so trying to list them manually would be fruitless. The better solution would be to route whatever device you use to stream Netflix outside the VPN tunnel. Alternatively you could try a SmartDNS service without changing any VPN settings (though obviously this is an added cost. They’re typically in the $2-4/month range).
But you still have not answered PapaKip’s question. How does one “tell the router to use (or skip) the VPN for specific websites.” There are a number of websites which do not allow access when using Merlin on my ASUS RT-AC88U with IPVanish. Ticketmaster, Bank of America, etc. How can I turn off VPN just for those websites that gag when I have VPN enabled?
You can have to manually enter the IP address of each website in the policy routing rules and route that traffic to WAN instead of VPN. A better solution is to use our dual-router setup method and switch to the non-VPN network for websites that block them.
Do you have any recommendations on the best way to “find” the ip’s your devices are going to that you want to route around? If I really want to exclude amazon and amazon prime for example. Specifically I want my firesticks to be protected for everything but when I go to amazon prime video, where they fail.
It would be the same as the Netflix question above. How does one easily see in realtime where one’s devices are going…..the destination ip’s?
You’d probably have to run a packet sniffer like Wireshark on your wireless network to identify where your Firestick traffic is going. That’s some pretty advanced stuff, but if you’re really motivated you might be able to figure it out by watching a youtube tutorial or two.
I understand the above about how to route a single device through the vpn.
What is the Accept DNS Configuration setting above? How is it different and what should it be set to?
thanks!
‘Accept DNS Configuration’ lets your VPN provider dictate which DNS servers should be used by your router (overriding your manual settings). This option may not work with all VPN providers depending on their server configuration, but I usually set it to ‘strict’ as long it doesn’t cause a connection error with the vpn.
I have set up my ASUS with Merlin using OpenVPN, I am an Amazon customer and when you put a VPN client on the router like you show, it gets blocked by Amazon even though I am a US customer using US VPN servers. I have spent hours with the (very popular VPN company) and they cannot help me as we change servers back and forth. So I did what you mention and allowed my Roku to bypass the VPN. Now the problem is that I have a DNS leak.
I am pretty new to VPN’s and networking and from what I understand a DNS leak is not a good thing to have. How do I avoid the DNS leak this causes and still be able to access my Amazon Prime movies?
DNS leaks are a security leak, but they generally aren’t a large threat for most VPN-uses. Basically a leak occurs if your Internet Provider’s DNS servers are still being seeing what websites you visit. I haven’t had any DNS leak issues with any VPNs when using Merlin, but you can try 2 things to fix it:
1: Specify your VPNs DNS servers in the ASUSWRT WAN settings
2: In Your VPN configuration, try changing the ‘Accept DNS Configuration’ setting to ‘Strict’.
One or Both of those changes should definitely fix the issue.
I have been struggling since moving up to 384.6.
I have a single dedicated server that I assign through the vpn using the procedure described. It has worked flawlessly until the latest upgrade.
Now the vpn connected (?) machine is not being rerouted, nor is the kill switch operational. it was happily revealing my IP!!!. No indication that anything is wrong, except for log information.
The log is showing failure to add routes.
Jan 1 15:36:18 ovpn-client1[8506]: OpenVPN 2.4.6 arm-unknown-linux-gnu [SSL (OpenSSL)] [LZO] [LZ4] [EPOLL] [MH/PKTINFO] [AEAD] built on Jul 25 2018
Jan 1 15:36:18 ovpn-client1[8506]: library versions: OpenSSL 1.0.2o 27 Mar 2018, LZO 2.08
Jan 1 15:36:18 ovpn-client1[8507]: WARNING: No server certificate verification method has been enabled. See http://openvpn.net/howto.html#mitm for more info.
Jan 1 15:36:18 ovpn-client1[8507]: NOTE: the current –script-security setting may allow this configuration to call user-defined scripts
Jan 1 15:36:18 ovpn-client1[8507]: TCP/UDP: Preserving recently used remote address: [AF_INET]213.5.71.71:53
Jan 1 15:36:18 ovpn-client1[8507]: UDP link local: (not bound)
Jan 1 15:36:18 ovpn-client1[8507]: UDP link remote: [AF_INET]213.5.71.71:53
Jan 1 15:36:18 ovpn-client1[8507]: WARNING: this configuration may cache passwords in memory — use the auth-nocache option to prevent this
Jan 1 15:36:23 ovpn-client1[8507]: [PureVPN] Peer Connection Initiated with [AF_INET]213.5.71.71:53
Jan 1 15:36:25 ovpn-client1[8507]: TUN/TAP device tun11 opened
Jan 1 15:36:27 ovpn-client1[8507]: ERROR: Linux route add command failed: external program exited with error status: 2
Jan 1 15:36:27 ovpn-client1[8507]: ERROR: Linux route add command failed: external program exited with error status: 2
Jan 1 15:36:27 openvpn-routing: Configuring policy rules for client 1
Jan 1 15:36:28 openvpn-routing: Tunnel re-established, restoring WAN access to clients
Jan 1 15:36:28 ovpn-client1[8507]: Initialization Sequence Completed
The most disturbing part is that the kill switch was not active either.
I can’t seem to get any more info than that log.
If you have any ideas of things to try, I sure would appreciate anything you could offer!
Thanks
Which VPN provider were you using? Occasionally I’ve seen issues with certain VPN’s having bad routing rules on their own servers which causes problems. Another thing worth trying is you can always roll-back to a previous Merlin firmware and see if that fixes the issue you’re experiencing (bugs do happen, even in official releases).
Hi, I was wondering if you could help me out with a setup just like this?
I happen to have Advanced Tomato and want to use an OpenVPN connection for specific websites.
I can set this up using the routing policy just fine. Now I would also like a kill switch for that, without having all my devices being enforced to use the VPN.
Could you help me set this up?
I’ve been testing out Advanced Tomato recently and it appears the routing policy rules don’t work properly. I think this is a known bug.
Hello, thank you for this tutorial. The” route all local IP’s through the VPN, we need to use CIDR Notation” method is not working for the USB tool: download master. Can you maybe explain how I can run download master with a VPN and kill switch if possible. Thanks in advance.
It appears this is a known issue with Download Master and can’t be made to work. The linked forum thread includes instructions on how to make this work with Transmission client instead of Download Master.
I have set-up L2TP as OpenVPN is too slow on my AC66U router. Speeds are not even comparable however there is no way that I know of to bypass L2TP for my voip phone as I get dial tone but can’t make any calls. Any idea’s on how to manually configure this outside of using OpenVPN (which is not an option for me). I am fairly technical so help would be appreciated.
The feature you’re describing is ‘Selective Routing‘ which is available on the 3rd-party Merlin ASUSWRT firmware. Unfortunately it only works with OpenVPN, not L2TP.
Since you’re using a single-core router (not powerful enough for OpenVPN) you may want to try our dual-router setup option, and route the VOIP phone to the primary router.
Hi, I’m using the latest ASUS-Merlin firmware and have successfully configured my VPN and routing using your tutorial here. My challenge is I have 2 VPN servers defined. VPN1 for local access (faster) and VPN2 connects to a server overseas for EU streaming. I may even want VPN3 for torrent…
How do I/Is it possible to route certain devices through VPN1, others through VPN2 and the rest to WAN?
Thanks
Sure, with the Merlin firmware you can actually run 2 VPN tunnels simultaneously. Each VPN has their own policy routing rules, so you can choose which IPs to route through each.
Please I would like you to help me out. Am using ASUS RT-86U now change toASUS Merlin firewall- I followed your configuration and found out my interface is not the same as yours description settings configuration.
My main purpose of changing is to use killswitch. Please can you help me to set the configuration settings right because that is were am having difficulties.
The most likely issue is your subnet is different than the one shown in the tutorial (192.168.138.x). Run ipconfig from the command line (if using a PC) to see what the IP address of your device is. Then add that IP to the list of devices to route inside or outside of the VPN.
Hi, I watched all your video and it was brilliant, so I went on “Private Internet Access” to get the config file in the “Downloads” tab so that I can upload in to my Asus router. so my question is “Do I need to pay when I upload the config file in to my router”, because one min the downloads look free then on the “Sign Up” tab it says to pay. It’s confusing.
Thanks in Advance
You won’t be able to use the VPN configs without a paid account. Each VPN connection requires a username/password to connect, which you can’t get without a subscription.
Hi,
If you enable the kill switch, will the VPN connection restore itself in the event it drops? Or do you need to manually restart the VPN ?
If your VPN software has an auto-reconnect option, it will restart automatically. Otherwise you will need to manually connect.
Question: You can add devices to the policy rules, but I noticed once added, it just adds the device’s IP.If you’re running DHCP, is this an issue? You make no mention of MAC and IP address binding (I went ahead and did it anyway). My router is set to reboot at 5 am daily, I’d hate to have a device being blocked by VPN and not knowing why all of a sudden
I’m not certain, but I think it may actually bind to the device’s MAC address, but displays the IP address. You could run a test, reboot the router and if your devices receive a new IP address, see if they still show in the policy rules under the new IP.
This guide is fantastic, thank you for taking the time to write it up, much appreciated!
I’ve run into an issue where I’m tried to exclude a device from going through the OpenVPN. I followed the instructions for adding the device and its IP and making sure its routed through the WAN as opposed to the VPN. I then rebooted the router and then the device itself.
When I log into the device, fire up a browser and go to https://www.whatsmyip.org/ I expect to see the IP provided by the ISP but instead I’m seeing the IP provided by the VPN service.
Any suggestions as to what I may have mis-configured?
It’s hard to know without seeing your setup, but my two suggestions are:
1) make sure policy rules are turned ON.
2) Make sure the device rule is after the ALL rule, routing the entire subnet to the VPN
3) Clear your browser cache and rerund the IP check in a private browsing window. Sometimes you’re just seeing a cached result but it’s actually working properly.
Speed reduces issue. Hi. I have an Asus RT-AC3100 on a VPN. When I reboot it, my speeds are around 32Mbps. VPN off, over 300Mbps. Over a 24 hour period, the VPN speed slows down to 15 to 22 Mbps. Reboot it and speed jump back up to 32Mbps. Any suggestions on how to maintain the higher speeds without reboot?
I think there’s a good chance this is caused by your VPN provider’s configuration or server architecture, rather than the router. They may throttle connections that have been open a long time or transferred a lot of data.