
If you are a frequent (or even casual) bittorrent user, you should absolutely be encrypting your torrent traffic. Torrent encryption has several privacy advantages including:
- Avoid torrent throttling or traffic monitoring by your internet provider
- Possibly increase download speeds (by blocking throttling)
- Disguise your torrent traffic for 3rd-party monitoring (network admin, school, etc)
Encryption vs. Anonymization: It is important to note that ‘encrypting’ your torrents is only a small part of a torrent anonymization strategy. Encryption won’t hide your torrent IP address, which is the #1 way torrent activity is monitored (because your IP is visible to all torrent peers). You should use this guide in conjunction with a torrent-friendly VPN or torrent proxy to achieve seriously private torrent downloads.
Introduction and concepts
Here’s a brief overview of what protocol encryption means, and what it actually does for your torrent traffic.
We’ll also discuss the 2 primary methods of encrypting torrent traffic (one of which is much stronger and more secure).
What is encryption
Dictionary.com defines ‘Encryption’ as the act of:
In other words, it scrambles or encodes your traffic in a way that it can’t be understood without knowing how to decrypt it which is done with a secret key known only to your computer. This allows you to securely transfer torrent data between trackers and peers without your ISP be being able to read it (or possibly even know that it’s torrent traffic at all).
Two methods of torrent encryption:
There are 2 methods you can use:
- VPN/Virtual Private Network – strongest possible encryption and full peer availability
- Built-in protocol encryption – available in most desktop torrent clients, but is less secure and will reduce the number of available peers.
A VPN is definitely the best option as we’ll explain, because of the difference in how the encryption is applied. To see why, we’ll examine how each option works:
Built-In Encryption (Inside your torrent client)
Most torrent clients include a ‘protocol encryption’ option. This will allow you to make encryption an available option, and some clients allow you to force encrypted connections to peers. This sounds great (because it’s totally free) but there are drawbacks to this method:
- Reduced Peer Availability: If you don’t choose to ‘force’ encryption, then most of your peer connections will be made unencrypted (defeating the purpose). If you do force encryption, then the number of available peers will drop significantly (limited to only other peers that allow encryption). This can negatively affect torrent speeds, or even make downloading the complete file impossible.
- Weak encryption algorithm: The bittorrent protocol uses the RC4 encryption cipher with an encryption key strength of between 60-80 bits (which is quite weak compared to AES which is the standard for OpenVPN traffic).
- Obfuscation Not Effective against torrent-blocking technology: The torrent encryption protocol is designed to help torrent traffic survive DPI inspection and slip through torrent-blocking firewalls. But Sandvine (a company that builds enterprise-level firewalls for ISPs) can reportedly identify and block most bittorrent traffic despite protocol encryption.
- May encrypt data ‘header’ not full stream: Each torrent client (Vuze, uTorrent, Tixati, etc.) chooses it’s own encryption implimentation. And some only encrypt the ‘headers’ of the data packets, not the contents or payload. This makes it trivially easy to identify torrent traffic by inspecting the message payload. Some clients like uTorrent and Vuze do offer full stream encryption.
VPN Encryption
The built-in protocol encryption in your torrent client encrypts each connection on a peer-by-peer basis. This means it’s managing several (possibly hundreds) of weak encrypted connections simultaneously.
A Virtual Private Network encrypts your traffic as a whole, not just torrent traffic. And it does so using extremely strong AES encryption, which can’t be inspected or decrypted by your Internet Provider or network firewall.
No Setup Required: Unlike your torrent client’s encryption, a VPN doesn’t require you to change (or screw up) any manual settings in your torrent software. It’s just 1-click to connect and it just works.
Best Options: We’ll discuss or recommended VPNs in the next section, but they’re all from our list of top p2p/torrent VPNs.
How to encrypt your torrents with a VPN
What you’ll need:
- Any torrent client (uTorrent, Vuze, Flud, Tixati, Deluge, etc…)
- A zero-log VPN service that supports torrenting
Recommended VPN Providers:
These are VPN’s that we have all personally tested. They are are all zero-log or keep only connection logs for 24 hours or less. All are fully torrent-compatible and several (PIA, IPVanish, and NordVPN) even include a SOCKS proxy for optional secondary protection.
| Rank | Company | Logging Policy | Best Offer (monthly) | Details |
|---|---|---|---|---|
1 | No Logs | $6.49 (Save 20%) | Visit SiteRead Review |
|
2 | No Logs | $3.29 (Save 72%) | Visit SiteRead Review |
|
3 | No Logs | $3.33 | Visit SiteRead Review |
|
4 | N/A | $8.32 | Visit SiteRead Review |
|
5 | 1 day | $4.83 | Visit SiteRead Review |
Setting up the encryption:
Steps:
- Sign up for a VPN, download and install the included software
- Open the VPN app
- Choose a server location (we recommend Netherlands, Switzerland, or Canada)
- Click ‘Connect’
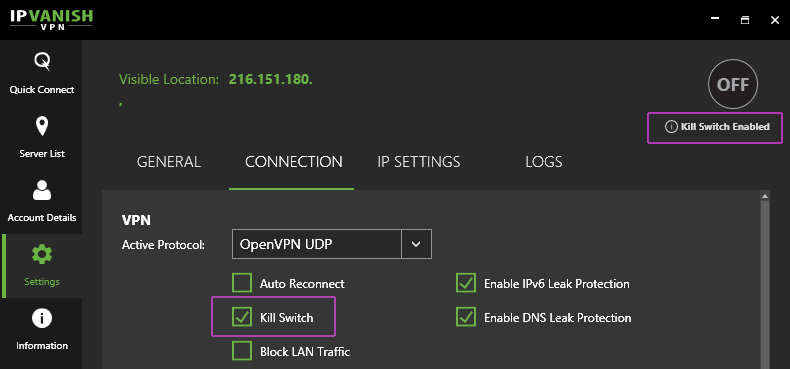
- Turn on the VPN Kill-switch for added security (optional)
- Open your torrent client and start torrenting
You can see just how easy this is using IPVanish’s desktop (or mobile) VPN software:
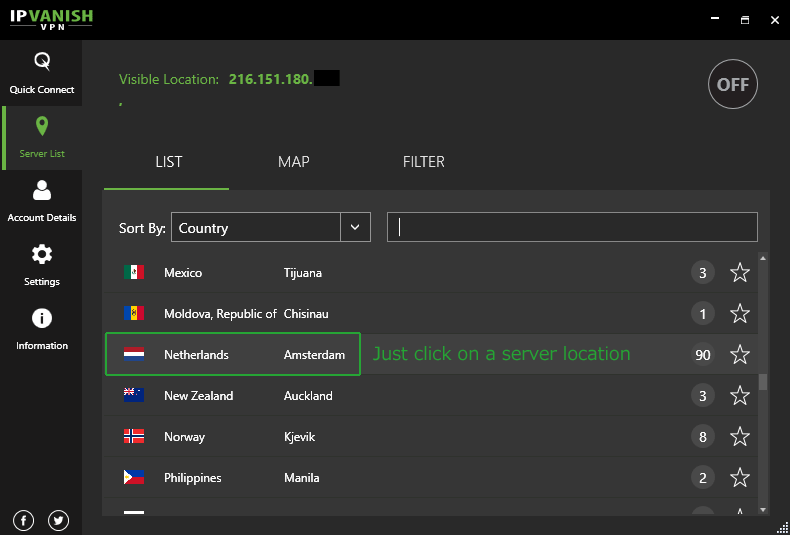
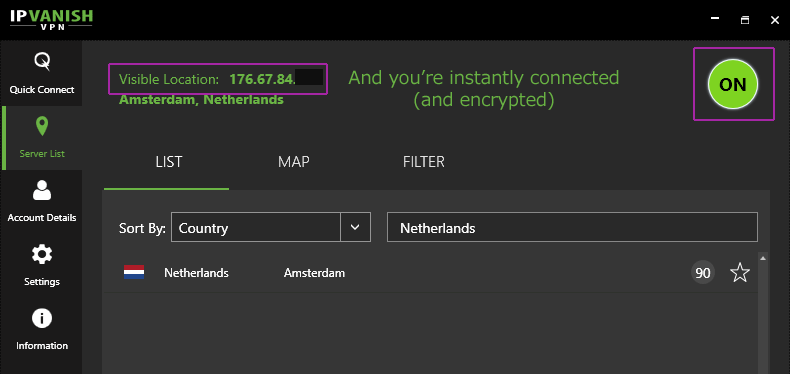
That’s it. One click and you’re set. You can also turn on the kill-switch which will prevent your real IP address from leaking if the VPN connection fails.
Using your torrent-clients ‘Built-in’ encryption feature
Reminder: This method is not as secure as using a VPN. It may help you avoid throttling issues with some ISPs, but isn’t good for much else. Importantly, it does nothing to anonymize your torrent IP address.
Weaknesses of this method:
- Weak RC4 encryption cipher
- Some implementations don’t encrypt data, only the packet ‘header’
- If you ‘Force’ encryption, you will lose some peers (and probably speed)
Note: We’ll only be showing the ‘maximum’ encryption settings for each torrent client. Anything less than ‘forced’ encryption (to all peers) will mean that some connects aren’t encrypted. That defeats the whole purpose.
Finally, there is no need to use this method if you’re already using a VPN for encryption. It’s redundant, adds no security, and will just slow your speeds.
Instructions by torrent client:
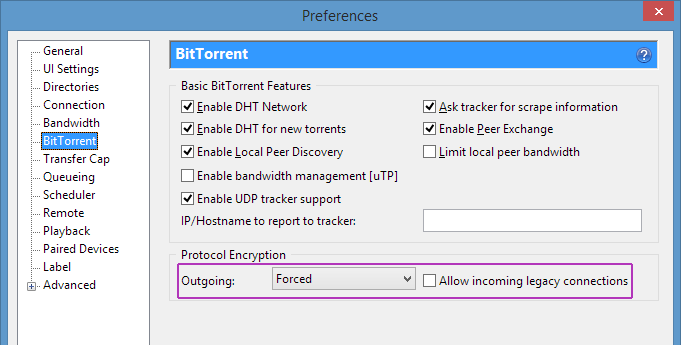
uTorrent/BitTorrent Encryption settings:
- Go to: Options > Preferences > Bittorrent (tab) > Protocol Encryption
- Choose ‘Forced’ for outgoing encryption.
- Click ‘apply’
Vuze/Azureus
- Go to: Tools > Options > Connection > Transport Encryption
- Enable ‘require encrypted transport’
- Set minimum encryption level to RC4
- Optional: Use the ‘Cryptoport’ extension to block some unencrypted tracker communications
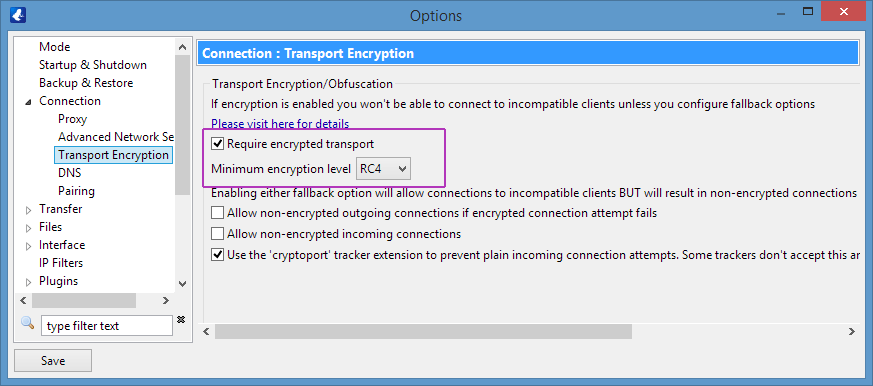
If you want you can chose to ‘allow non-encrypted connections’ as a fallback (for poorly seeded torrents) but remember that this means some peer connections won’t use encryption. Your ISP could monitor, throttle, or block them.
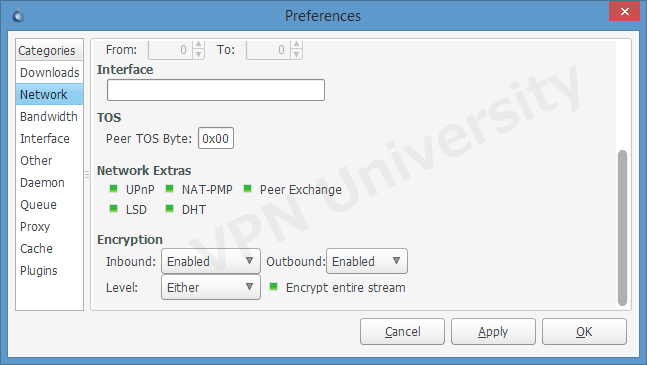
Deluge Encryption
Deluge gives you a bit more control over the encryption settings than some other torrent software.
Go to: Edit > Preferences > Network > Encryption (bottom section)
There several encryption options, but they really boil down to 2 basic profiles:
- Enabled encryption (will still connect to some non-encrypted peers)
- Forced Full-stream encryption (strongest/best)
For ‘Enabled’ Encryption choose:
- Inbound: Enabled
- Outbound: Enabled
- Level: Either
- Encrypt entire stream: Yes
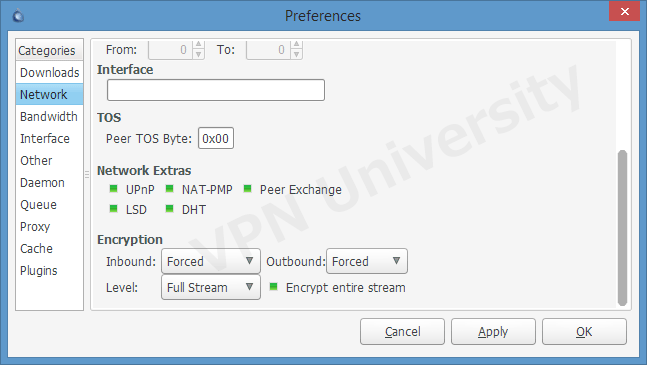
For ‘Forced’ full-time, full-stream encryption:
- Inbound: Forced
- Outbound: Forced
- Level: Full Stream
- Encrypt Entire Stream: Yes
QBittorrent Encryption Settings
To access QBittorrent’s encryption settings,
Go to: Tools > Options > Bittorrent (left menu) > Privacy (top section) > Encryption mode
- Encryption Mode: Require encryption
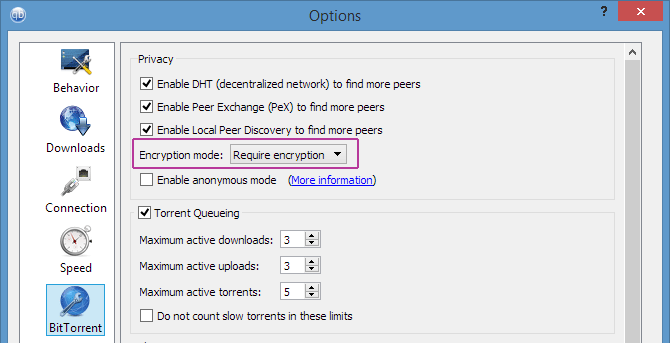
Note: The Qbittorrent Wiki doesn’t clarify the encryption settings. Nor does it say whether it’s up/down (or just one way) or full-stream or just an encrypted header. If you want serious encryption with QBittorrent, choose one of these VPNs.
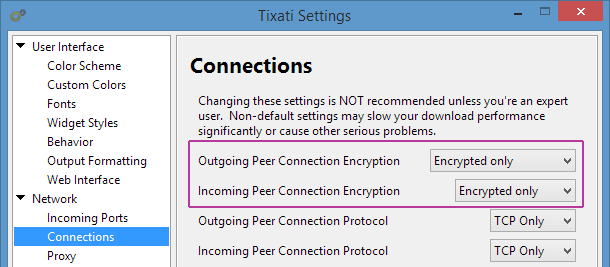
Tixati
To access Tixati’s encryption settings, go to:
Settings (Gear Icon) > Network (Left Menu) > Connections
For ‘optional’ encryption:
- Outgoing Peer Encryption: Encrypted Preferred
- Incoming Peer Encryption: Encrypted Preferred
For ‘Forced’ encryption:
- Outgoing Peer Encryption: Encrypted Only
- Incoming Peer Encryption: Encrypted Only
Conclusion and further reading:
We’ll be adding more torrent clients (like transmission) in the future as time allows. In the meantime, you should be able to apply the same principles shown in this guide to any other torrent software that offers an encryption feature.
Just remember that the built-in option is quite limited in strength and effectiveness. If you’re up against a firewall or ISP that actively blocks torrents, you’ll need to get a VPN like IPVanish. Try this 20% off coupon and get security and torrent privacy in one awesome tool.
If you have any questions or suggestions, please leave them in the comments. Please follow us @vpnuniversity for security tips, VPN tutorials, and special discount offers.


I disagree that turning on Protocol Encryption will reduce the number of peers. I believe quite the opposite is true. Most torrent users force protocol encryption as I have done for 15-20 years, so if you do not have protocol encryption at least turned on you will be restricted to users in the swarm that do not force it, which IMO is much lower number of users than those that do.
Any peers that use ‘forced’ encryption will still connect to peers that only have encryption ‘enabled’ but not forced. So the flexible setting will give you the most peers by allowing you to connect to both encrypted and unencrypted peers. You’re right, though, the majority of users do have some sort of encryption enabled.
Great article. Do you have any experience or information for torrent clients on android that support protocol encryption? Thx
I’m 100% certain that Flud does (my favorite Android client). I think tTorrent does as well but can’t remember offhand.
I should know this, but is there any gain in using both a VPN and the onboard encryption of Utorrent(or any other client)?
Nope, just use the VPN. You should leave uTorrent encryption set to ‘enabled’, however, to maximize peer availability.